Cybersecurity Best Practices for Businesses
Cybersecurity Best Practices for Businesses
A Comprehensive Guide to Protecting Your Organization in the Digital Age
Cybersecurity is not only an IT issue it is a business survival issue. In the globalized environment, one attack will cost millions, ruin reputations, and bring the operations to a standstill. This manual is a profound, practical roadmap to any business regardless of size. Lets learn more about Akshay Sharma AVS Security .
The Growing Threat Landscape
The digital revolution has offered something of unparalleled opportunity – but also of unprecedented risk. Cybercriminals cease to be a basement dwelling solo hacker, now they are well-organized, well-funded criminal groups, and even nation state groups, attacking businesses of all sizes and all industries.
📈 Global Cybercrime Cost Projection (2019–2025)
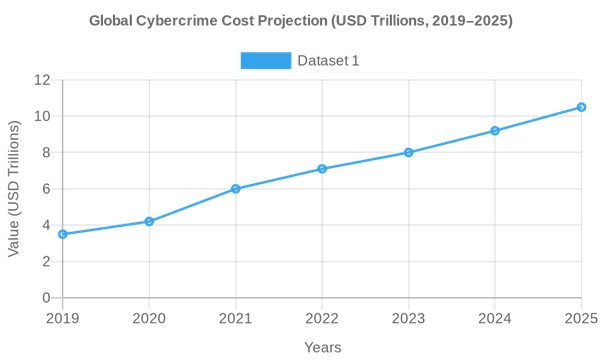
The world cybercrime is set to amount to a staggering USD 10.5 trillion per year by 2025 , as compared to 2019, USD 3.5 trillion USD , that is 200 percent higher in half a decade. This is an astounding number that encompasses:
- 💸 Direct financial losses from theft and fraud
- 🔧 Operational disruption and downtime costs
- 🗂️ Data destruction and recovery expenses
- 🧠 Intellectual property theft
- 🏛️ Regulatory fines and legal fees
- 📉 Reputational damage and loss of customer trust
🚨 Top Cyber Threats Facing Businesses (2024)
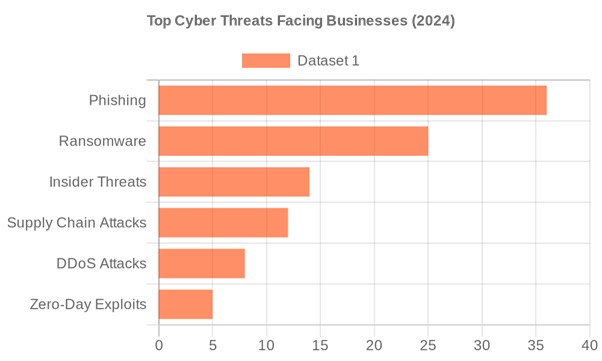
| Threat | Share | Description |
| 🎣 Phishing | 36% | Deceptive emails/messages tricking users into revealing credentials |
| 🔒 Ransomware | 25% | Malware that encrypts data and demands payment for release |
| 🕵️ Insider Threats | 14% | Malicious or negligent employees leaking or misusing data |
| 🔗 Supply Chain Attacks | 12% | Compromising vendors/partners to infiltrate target organizations |
| 💥 DDoS Attacks | 8% | Overwhelming servers to take down services |
| 🕳️ Zero-Day Exploits | 5% | Attacks exploiting unknown software vulnerabilities |
💰 Average Cost of a Data Breach by Industry (2024)
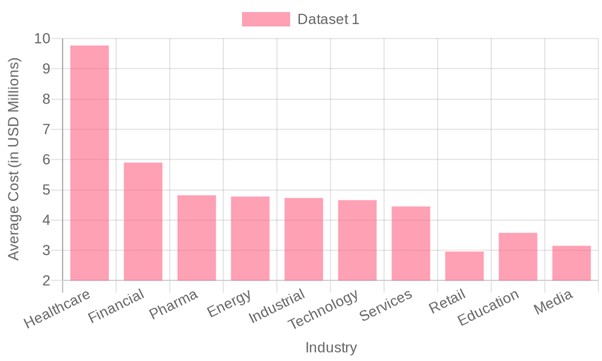
The average cost of a breach in healthcare is 9.77 million which is almost twice the breach cost in the financial sector of 5.90 million . These figures highlight why industry-specific cybersecurity strategies are critical — the stakes are not uniform across sectors. According to Akshay Sharma Kriti Nagar</a> this cost may be higher in upcoming days .
Implement Multi-Factor Authentication (MFA)
The use of Multi-Factor Authentication (MFA) is generally considered to be the most effective security control of any in a business. It also compels users to authenticate themselves using two or more autonomous ways of authentication before access.
🔑 The Three Factors of Authentication:
| Factor | Type | Examples |
| Something you know | Knowledge | Password, PIN, security question |
| Something you have | Possession | Authenticator app, hardware token, SMS code |
| Something you are | Inherence | Fingerprint, facial recognition, retina scan |
✅ MFA Implementation Best Practices:
- Enable MFA on all business accounts — email, cloud services, VPNs, admin portals, and financial systems
- Prioritize authenticator apps (Google Authenticator, Microsoft Authenticator, Duo) over SMS-based OTPs, which are vulnerable to SIM-swapping attacks
- Enforce phishing-resistant MFA (FIDO2/WebAuthn hardware keys) for privileged accounts and executives
- Implement Adaptive MFA that triggers additional verification based on risk signals (unusual location, new device, off-hours login)
- Periodically check on the users that are set to have MFA and implement the same to all users, including contractors and vendors . Create a safer MFA recovery process – lost device processes must be as safe as MFA is.
- Establish a secure MFA recovery process — lost device procedures should be as secure as the MFA itself
💡 Microsoft reports that MFA blocks over 99.9% of automated account compromise attacks . Despite this, many businesses still haven’t fully deployed it.
Employee Security Awareness Training
Human error is the number one cause of data breaches, with more than 82 percent of data breaches being caused by human errors as reported in Data Breach Investigations Report by Verizon. Your employees are at the same time your best asset and at the same time your weakness.
🎯 What Effective Security Training Covers:
🎣 Phishing Awareness
- How to identify suspicious sender addresses, urgency tactics, and malicious links
- The difference between spear phishing (targeted), whaling (executive-targeted), and vishing (voice phishing)
- What to do when you receive a suspicious email — report, don’t click
🔐 Password Hygiene
- Use of password managers (Bitwarden, 1Password, LastPass) to generate and store complex passwords
- Never reuse passwords across accounts
- Use passphrases of 16+ characters for critical accounts
- Understand why periodic forced password changes can be counterproductive
📱 Social Engineering Defense
- Recognize pretexting, baiting, and quid pro quo attacks
- Verify identities before sharing sensitive information — even with apparent colleagues
- Be wary of urgency and authority manipulation tactics
🖥️ Safe Computing Habits
- Lock screens when stepping away from workstations
- Never use personal devices for work without MDM (Mobile Device Management)
- Avoid public Wi-Fi without a VPN
- Report lost or stolen devices immediately
✅ Training Program Best Practices:
- Conduct quarterly training sessions with updated content reflecting current threats
- Run monthly phishing simulations to test real-world awareness
- Gamify training with leaderboards and rewards to boost engagement
- Tailor training by role — finance teams need different training than developers
- Track metrics: click rates on simulated phishing, training completion rates, incident reporting rates
- Establish a no-blame reporting culture — employees should feel safe reporting mistakes
📊 Organizations with mature security awareness programs reduce phishing susceptibility by up to 70% and see a significant reduction in breach-related costs.
Patch Management & Software Updates
Unpatched vulnerabilities are the open doors cybercriminals walk through. The infamous WannaCry ransomware attack in 2017 infected over 200,000 systems in 150 countries — exploiting a Windows vulnerability for which a patch had been available for two months .
⚠️ The Patching Problem:
- The average time to patch a critical vulnerability is 60–150 days
- Attackers begin exploiting new vulnerabilities within hours of public disclosure
- Many businesses run legacy systems that can no longer receive patches
- Shadow IT (unauthorized software) creates unmanaged patch gaps
✅ Patch Management Best Practices:
- Establish a formal Patch Management Policy with defined SLAs:
- Critical patches: 24–72 hours
- High severity: 7 days
- Medium severity: 30 days
- Low severity: 90 days
- Use automated patch management tools (WSUS, Ivanti, ManageEngine, Qualys)
- Maintain a complete software and hardware inventory — you can’t patch what you don’t know about
- Test patches in a staging environment before production deployment
- Prioritize internet-facing systems and those handling sensitive data
- Develop a compensating controls strategy for systems that cannot be patched (network segmentation, enhanced monitoring)
- Regularly scan for vulnerabilities using tools like Nessus, Rapid7, or Qualys
Network Security
Your network is the central nervous system of your business. A compromised network means compromised everything — data, operations, communications, and customer trust.
🏗️ Network Security Architecture Layers:
🔥 Firewalls & Perimeter Defense
- Deploy Next-Generation Firewalls (NGFW) with deep packet inspection, application awareness, and integrated IDS/IPS
- Implement Web Application Firewalls (WAF) to protect customer-facing web applications
- Configure strict ingress and egress filtering rules
- Regularly audit and review firewall rules — remove outdated rules that expand attack surface
🔀 Network Segmentation
- Divide your network into security zones : DMZ, internal network, management network, guest network
- Isolate critical systems (financial, HR, R&D) from general employee access
- Segment IoT devices onto their own VLAN — smart TVs and printers shouldn’t share a network with your ERP system
- Use micro-segmentation in virtualized and cloud environments
📡 Wireless Security
- Use WPA3 encryption for all wireless networks
- Maintain separate SSIDs for corporate devices, guests, and IoT
- Disable WPS (Wi-Fi Protected Setup) — it’s a known vulnerability
- Conduct regular wireless site surveys to detect rogue access points
- Implement 802.1X authentication for enterprise wireless access
👁️ Network Monitoring
- Deploy SIEM (Security Information and Event Management) solutions (Splunk, Microsoft Sentinel, IBM QRadar)
- Implement Network Detection and Response (NDR) tools for behavioral anomaly detection
- Establish 24/7 monitoring — either in-house SOC or managed MSSP
- Define and regularly test alerting thresholds to minimize alert fatigue
Endpoint Protection
Every device that connects to your network — laptops, desktops, smartphones, tablets, servers — is an endpoint and a potential entry point for attackers. Get more ideas by Akshay Sharma AVS News .
🛡️ Modern Endpoint Security Stack:
| Tool | Purpose |
| EDR (Endpoint Detection & Response) | Real-time threat detection, investigation, and automated response |
| Antivirus/Anti-malware | Signature and behavior-based malware detection |
| DLP (Data Loss Prevention) | Prevent unauthorized data exfiltration |
| MDM (Mobile Device Management) | Enforce policies on mobile and remote devices |
| Application Whitelisting | Only allow approved applications to run |
| Full Disk Encryption | Protect data on lost/stolen devices (BitLocker, FileVault) |
✅ Endpoint Security Best Practices:
- Deploy EDR solutions (CrowdStrike Falcon, Microsoft Defender for Endpoint, SentinelOne) on all endpoints
- Enforce full disk encryption on all laptops and mobile devices
- Implement application control to prevent unauthorized software installation
- Use Mobile Device Management (MDM) to enforce security policies, enable remote wipe, and manage BYOD devices
- Disable AutoRun/AutoPlay features to prevent USB-based malware
- Implement USB port controls — restrict or block unauthorized removable media
- Regularly conduct endpoint compliance audits to ensure all devices meet security baselines
Data Backup & Incident Response Planning
Even the most fortified organizations can be breached. The difference between a recoverable incident and a business-ending catastrophe often comes down to preparation .
📦 The 3-2-1-1-0 Backup Rule (Modern Standard):
| Rule | Meaning |
| 3 | Maintain 3 copies of your data |
| 2 | Store on 2 different types of media (e.g., disk + tape) |
| 1 | Keep 1 copy offsite or in the cloud |
| 1 | Keep 1 copy offline/air-gapped (ransomware-proof) |
| 0 | Zero errors — verify backups with regular restore tests |
📋 Incident Response Plan (IRP) — The 6 Phases:
markdown
Copy
- PREPARATION → Policies, tools, team roles, training
- IDENTIFICATION → Detect and confirm the incident
- CONTAINMENT → Isolate affected systems to prevent spread
- ERADICATION → Remove malware, close vulnerabilities
- RECOVERY → Restore systems from clean backups
- LESSONS LEARNED → Post-incident review and improvements
✅ Backup & IR Best Practices:
- Test backups with full restore drills at least quarterly
- Maintain immutable backups that cannot be altered or deleted (even by admins)
- Define Recovery Time Objectives (RTO) and Recovery Point Objectives (RPO) for all critical systems
- Conduct tabletop exercises simulating ransomware, data breach, and DDoS scenarios
- Establish a 24/7 incident response hotline and clear escalation paths
- Maintain relationships with external IR firms (Mandiant, CrowdStrike Services) for major incidents
- Prepare pre-approved communication templates for breach notifications to customers, regulators, and media
💰 Organizations with a tested incident response plan save an average of $2.66 million per breach compared to those without one (IBM Cost of a Data Breach Report).
Cloud Security & Access Management
📊 Cybersecurity Spending Growth by Segment (2022–2024)
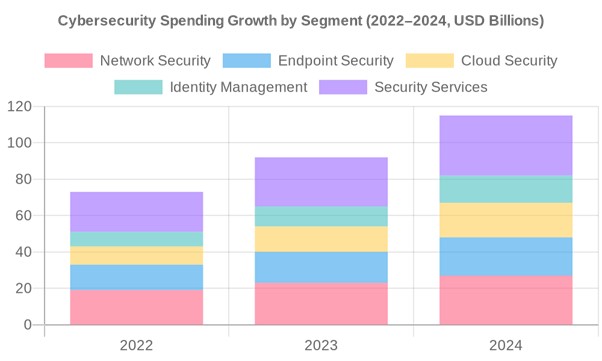
Cloud security spending has grown from $10B in 2022 to $19B in 2024 , reflecting the rapid migration of business workloads to cloud environments. As businesses embrace AWS, Azure, Google Cloud, and SaaS applications, securing these environments has become paramount.
☁️ The Shared Responsibility Model:
Understanding who is responsible for what in cloud security is fundamental:
| Responsibility | Cloud Provider | Customer |
| Physical infrastructure | ✅ | ❌ |
| Hypervisor/virtualization | ✅ | ❌ |
| Network controls | Shared | Shared |
| Operating system | ❌ | ✅ |
| Application security | ❌ | ✅ |
| Data classification | ❌ | ✅ |
| Identity & access management | ❌ | ✅ |
✅ Cloud Security Best Practices:
- Apply Least Privilege Access — users and services should have only the minimum permissions needed
- Use Cloud Security Posture Management (CSPM) tools to continuously audit cloud configurations
- Enable encryption for all data at rest and in transit — manage your own encryption keys where possible
- Implement Cloud Access Security Brokers (CASBs) to monitor and control cloud application usage
- Regularly review and remove unused cloud resources, accounts, and permissions (cloud sprawl is a real risk)
- Enable CloudTrail/Audit Logs and centralize them in your SIEM
- Use Infrastructure as Code (IaC) security scanning to catch misconfigurations before deployment
- Implement multi-region redundancy for critical workloads
Zero Trust Architecture
The traditional “castle and moat” security model — trust everything inside the network — is dead. Zero Trust operates on a simple but powerful principle: “Never trust, always verify.”
🔑 Zero Trust Core Principles:
- Verify explicitly — Always authenticate and authorize based on all available data points (identity, location, device health, service/workload, data classification, anomalies)
- Use least privilege access — Limit user access with just-in-time and just-enough-access, risk-based adaptive policies, and data protection
- Assume breach — Minimize blast radius, segment access, verify end-to-end encryption, use analytics to get visibility and drive threat detection
🏗️ Zero Trust Implementation Pillars:
| Pillar | Key Technologies |
| Identity | MFA, IAM, Privileged Access Management (PAM) |
| Devices | EDR, MDM, device compliance policies |
| Network | Micro-segmentation, SD-WAN, ZTNA |
| Applications | App-level access controls, WAF, API security |
| Data | DLP, encryption, data classification |
| Visibility | SIEM, SOAR, User & Entity Behavior Analytics (UEBA) |
🏢 Major enterprises like Google (BeyondCorp), Microsoft, and the U.S. Federal Government have mandated Zero Trust adoption — it’s quickly becoming the industry standard.
Supply Chain Security
The SolarWinds attack (2020) and Kaseya ransomware attack (2021) demonstrated that even well-secured organizations can be compromised through their trusted vendors and software suppliers .
✅ Supply Chain Security Best Practices:
- Conduct thorough vendor security assessments before onboarding — use standardized questionnaires (SIG, CAIQ)
- Include cybersecurity requirements in all vendor contracts and SLAs
- Implement third-party risk management (TPRM) programs with continuous monitoring
- Apply least privilege to all third-party integrations and API connections
- Maintain a Software Bill of Materials (SBOM) for all software used in your environment
- Monitor for open-source vulnerabilities in your software dependencies (Snyk, Dependabot)
- Conduct penetration testing that includes supply chain attack scenarios
- Have a vendor incident response plan — know what to do if a key vendor is breached
Cyber Insurance
Cyber insurance has evolved from a niche product to a business necessity . As breach costs soar, insurance provides a critical financial safety net.
📋 What Cyber Insurance Typically Covers:
| Coverage Type | Description |
| First-Party Coverage | Direct losses: data recovery, business interruption, ransomware payments |
| Third-Party Liability | Claims from customers/partners affected by your breach |
| Regulatory Fines | GDPR, HIPAA, and other regulatory penalties |
| Crisis Management | PR, legal, and notification costs |
| Cyber Extortion | Ransomware negotiation and payment assistance |
| Forensic Investigation | Cost of breach investigation and root cause analysis |
✅ Cyber Insurance Best Practices:
- Work with a specialist cyber insurance broker who understands the technical requirements
- Understand policy exclusions carefully — many policies exclude nation-state attacks or unpatched systems
- Implement the security controls insurers require — MFA, EDR, and backups are often mandatory
- Conduct an annual cyber risk assessment to ensure coverage remains adequate
- Test your claims process before you need it — know exactly who to call and what documentation is needed
Compliance & Regulatory Frameworks
Cybersecurity compliance is both a legal obligation and a competitive advantage . Customers, partners, and investors increasingly demand evidence of strong security practices.
🗺️ Major Cybersecurity Frameworks & Regulations:
| Framework/Regulation | Applies To | Key Focus |
| NIST CSF 2.0 | All organizations | Comprehensive security framework (Identify, Protect, Detect, Respond, Recover, Govern) |
| ISO/IEC 27001 | All organizations | International information security management system standard |
| GDPR | EU data processors/controllers | Data privacy and protection for EU citizens |
| HIPAA | US healthcare organizations | Protection of patient health information |
| PCI-DSS v4.0 | Payment card processors | Security of cardholder data |
| SOC 2 Type II | SaaS/cloud providers | Security, availability, and confidentiality controls |
| CMMC 2.0 | US DoD contractors | Cybersecurity maturity for defense supply chain |
| NIS2 Directive | EU critical infrastructure | Network and information security requirements |
✅ Compliance Best Practices:
- Map your security controls to multiple frameworks simultaneously — there is significant overlap
- Use GRC (Governance, Risk, and Compliance) platforms (ServiceNow GRC, RSA Archer) to manage compliance efficiently
- Conduct annual internal audits and periodic third-party assessments
- Maintain evidence of compliance continuously — don’t scramble before audit time
- Appoint a dedicated CISO or compliance officer responsible for regulatory adherence
- Stay current on regulatory changes — the landscape evolves rapidly
Building a Security Culture
Technology alone cannot secure your business. A security-first culture — where every employee understands and embraces their role in protecting the organization — is the ultimate defense.
🏛️ Pillars of a Strong Security Culture:
👔 Leadership Commitment
- The CEO and board must visibly champion cybersecurity
- Include cybersecurity as a board-level agenda item with regular reporting
- Allocate adequate budget — security should never be the first line item cut
- Appoint a CISO with a direct line to the board
📣 Open Communication
- Create a psychologically safe environment for reporting security incidents — no blame, no punishment
- Celebrate security wins and recognize employees who report threats
- Share threat intelligence broadly — help employees understand what they’re defending against
- Publish a clear, accessible security policy that employees actually read
🔄 Continuous Improvement
- Conduct post-incident reviews with a focus on learning, not blame
- Track and trend security metrics over time
- Benchmark against industry peers using frameworks like BSIMM or CMMI
- Invest in security champions — employees in each department who advocate for security
Cybersecurity for Remote & Hybrid Work
The shift to remote and hybrid work has dramatically expanded the attack surface. Home networks, personal devices, and cloud applications have created new vulnerabilities that traditional perimeter security cannot address.
✅ Remote Work Security Best Practices:
🔒 Secure Connectivity
- Require VPN usage for all access to corporate resources
- Consider ZTNA (Zero Trust Network Access) as a more secure VPN replacement
- Implement split tunneling policies carefully — ensure corporate traffic is always protected
- Use DNS filtering to block malicious domains on all remote devices
🖥️ Device Security
- Enforce MDM policies on all devices used for work — corporate and BYOD
- Require full disk encryption on all remote endpoints
- Implement automatic screen lock after short periods of inactivity
- Provide secure home router guidelines to employees — change default passwords, enable WPA3
📧 Secure Collaboration
- Use end-to-end encrypted communication tools
- Train employees on video conferencing security — meeting passwords, waiting rooms, screen sharing controls
- Implement email security gateways with advanced anti-phishing and sandboxing
- Use Digital Rights Management (DRM) for sensitive documents shared externally
SMB Cybersecurity Investment Breakdown
💰 Where Businesses Are Investing
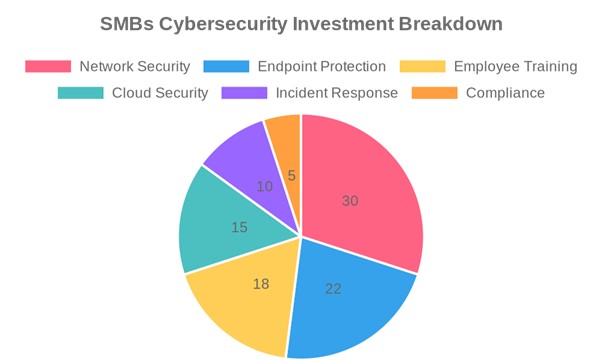
Smart businesses are allocating their cybersecurity budgets strategically across multiple domains. Network Security (30%) and Endpoint Protection (22%) dominate spending, but forward-thinking organizations are increasingly investing in Employee Training (18%) — recognizing that human risk is often the highest ROI investment.
✅ Part 16 — The Ultimate Cybersecurity Checklist
🔴 Critical Priority (Implement Immediately)
- Enable MFA on all accounts — email, cloud, VPN, admin portals
- Deploy EDR/antivirus on all endpoints
- Implement automated patch management with defined SLAs
- Establish regular data backups following the 3-2-1-1-0 rule
- Configure and test firewall rules
- Conduct phishing awareness training for all employees
- Implement network segmentation for critical systems
- Enforce strong password policies and deploy a password manager
🟠 High Priority (Implement Within 90 Days)
- Develop a formal Incident Response Plan (IRP)
- Deploy SIEM for centralized log monitoring
- Conduct a vulnerability assessment of all systems
- Implement least privilege access across all systems
- Establish a vendor risk management program
- Audit and secure cloud configurations
- Deploy email security gateway with anti-phishing
- Obtain cyber insurance coverage
🟡 Medium Priority (Implement Within 6 Months)
- Begin Zero Trust Architecture implementation
- Achieve relevant compliance certifications (ISO 27001, SOC 2)
- Implement UEBA for insider threat detection
- Develop a Business Continuity Plan (BCP)
- Conduct a penetration test by a qualified third party
- Establish a Security Operations Center (SOC) or engage an MSSP
- Implement DLP to prevent data exfiltration
- Appoint a CISO or security leader
🟢 Ongoing (Continuous Activities)
- Monthly phishing simulations
- Quarterly security training updates
- Annual penetration testing
- Continuous vulnerability scanning
- Regular backup restore tests
- Periodic tabletop exercises
- Annual cyber insurance review
- Continuous threat intelligence monitoring
🔑 Conclusion
Cybersecurity is not a destination — it is a continuous journey of improvement, adaptation, and vigilance . The threat landscape evolves daily, and so must your defenses. The businesses that thrive in the digital age will be those that treat cybersecurity not as a cost center, but as a strategic enabler — building trust with customers, protecting intellectual property, and ensuring operational resilience.
The 15 domains covered in this guide form a comprehensive, layered defense strategy . No single control is sufficient; true security comes from the depth and integration of multiple overlapping controls — what security professionals call Defense in Depth .
🚀 Where to Start:
- Assess your current security posture honestly
- Prioritize based on your highest risks and most critical assets
- Implement controls systematically, starting with the critical priority list
- Measure your progress with metrics and KPIs
- Improve continuously — review, test, and update regularly
“The question is no longer IF your business will face a cyber threat, but WHEN — and how prepared you’ll be when it arrives.”

Leave A Comment